Is trello.com Safe? Security Analysis for Atlassian
Check if trello.com is a scam or legitimate. Free security scan and reviews.
AI Summary
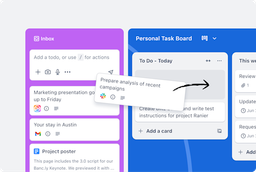
Trello, a product of Atlassian, is a leading SaaS platform focused on task and project management, enabling teams worldwide to organize and boost productivity through features like boards, inbox, planner, and automation. The website demonstrates a mature digital infrastructure leveraging modern technologies such as React and AWS hosting, with integrated AI capabilities enhancing user experience. Security posture is strong with HTTPS, reCAPTCHA, and cookie consent mechanisms, though explicit security headers could be further confirmed. Privacy compliance is robust, with clear policies and GDPR adherence. Overall, the site reflects a professional, trustworthy, and well-maintained digital presence aligned with enterprise standards.
Detected Technologies
🧠AI Business Intelligence
Technology stack, business insights, and market analysis powered by AI.
Business Intelligence
Market & Strategic Analysis
Trello operates in the technology sector, targeting teams and individuals seeking productivity tools. Its business model is subscription-based with tiered plans catering to various team sizes. The platform benefits from Atlassian's strong market position and brand recognition. Key competitive advantages include extensive integrations, automation, and AI-powered features. The company maintains a global user base and emphasizes ease of use and collaboration. Strategic partnerships and a comprehensive ecosystem support growth and customer retention.
Security Posture Analysis
Comprehensive Security Assessment
The website exhibits a high security maturity level with enforced HTTPS, use of reCAPTCHA to prevent abuse, and cookie consent management via OneTrust. No vulnerabilities or exposed sensitive data were detected in the analyzed content. However, the absence of explicit security policy pages and incident response contacts suggests room for improvement in transparency and readiness. Compliance with GDPR is evident through privacy policies and consent mechanisms. The security culture appears proactive but could benefit from publishing vulnerability disclosure and security.txt files.
Strategic Recommendations
Priority Actions for Security Improvement
Publish a dedicated security policy and incident response contact information to enhance transparency.
✨Observations
AI-powered comprehensive website and business analysis.
AI-Enhanced Website Analysis
Business Insights
Atlassian
Trello is a productivity tool that helps teams capture, organize, and manage tasks and projects from anywhere. It offers features like Inbox, Boards, Planner, automation, integrations, and templates to boost team efficiency.
excellent
consistent
Technical Stack
fast
excellent
good
good
Security Assessment
- HTTPS enforced
- Use of reCAPTCHA for forms
- Cookie consent mechanism
- No exposed sensitive data in HTML
- Use of Atlassian Intelligence for automation
Analytics & Tracking
Advertising & Marketing
Website Quality Assessment
Key Observations
Website is fully accessible with rich content and interactive features.
🛡️Security Headers
HTTP security headers analysis and recommendations.
Security Headers
HTTP security headers analysis
Missing Content-Security-Policy header
HIGHControls resources the browser is allowed to load
Missing Permissions-Policy header
MEDIUMControls browser features and APIs
Sensitive data may be cached
LOWCache-Control header should include "no-store" for sensitive pages
👤GDPR Compliance
Privacy and data protection assessment under GDPR regulations.
GDPR Compliance
Privacy and data protection assessment
No Cookie Policy found
HIGHGDPR requires clear information about cookie usage
No Cookie Consent Banner found
HIGHGDPR requires explicit consent for non-essential cookies
Privacy policy may not be GDPR compliant
MEDIUMPrivacy policy lacks explicit GDPR compliance elements
GDPR Compliance Analysis
🛡️NIS2 Compliance
Network & Information Security Directive compliance assessment.
NIS2 Compliance
Network & Information Security Directive
No information security framework found
HIGHNIS2 requires documented cybersecurity and information security measures
No vulnerability disclosure policy
MEDIUMNIS2 encourages coordinated vulnerability disclosure
No security policy documentation found
HIGHNIS2 requires documented cybersecurity governance and risk management
No incident response procedures found
HIGHNIS2 requires documented incident response and business continuity plans
No business continuity planning found
MEDIUMNIS2 emphasizes operational resilience and business continuity
No security contact information
HIGHNIS2 requires clear incident reporting channels
No vulnerability reporting mechanism
MEDIUMClear vulnerability reporting supports coordinated disclosure
No NIS2 reference found
LOWConsider explicitly mentioning NIS2 compliance efforts
📧Email Security
SPF, DKIM, and DMARC validation and email security assessment.
Email Security
SPF, DKIM, and DMARC validation
Complex SPF record
LOWToo many include statements can cause lookup limits
SPF Details
DKIM Selectors Found
DMARC Details
MTA-STS Details
🏆SSL/TLS Security
Certificate validity and encryption analysis.
SSL/TLS Security
Certificate validity and encryption analysis
Weak Protocols Supported
HIGHServer supports weak protocols: TLSv1.1
Certificate Transparency Not Implemented
LOWCertificate is not logged in Certificate Transparency logs
Partial SSL/TLS Assessment
LOWCompleted 3 of 4 security checks due to time constraints
Protocol Support
OCSP Status
📊DNS Health
DNS configuration and security assessment.
DNS Health
DNS configuration and security assessment
DNSSEC Not Enabled
MEDIUMDNSSEC is not configured for this domain
CAA Records Not Configured
LOWCertificate Authority Authorization (CAA) records not found
Domain Registration Details
DNS Records
DNSSEC Status
DNS Performance
SPF Analysis
⚡Network Security
Port scanning and network exposure analysis.
Network Security
Port scanning and network exposure analysis
Good Network Security Posture
LOWNo unnecessary services detected on common risky ports
🔧Technical Analysis
Detailed technical findings and analysis from AI assessment.
Technical Analysis
Comprehensive security assessment findings